| | |
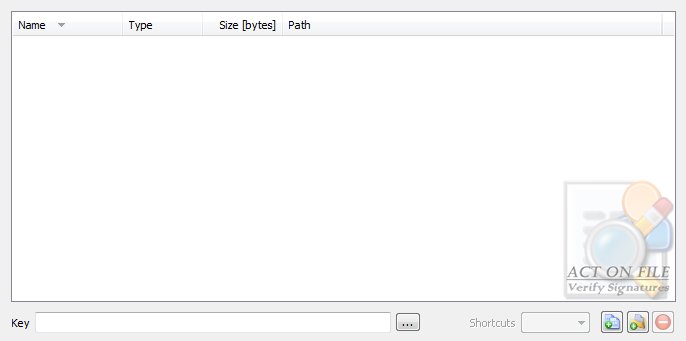
| Selection Controls |
 |
|
|
These controls are used to select and display the files and folders for the operation, and the authentication (public) key. In addition to the Add Files, Add Folders and Remove buttons, you can use the standard clipboard, drag and drop, and keyboard operations.
|
| Key | Enter the path to the authentication public (or private) key. Remember to keep Private Keys safe and secret until such time as they are to be destroyed using True Delete. |
| Shortcuts | Select the behavior of the functionality in respect to any shortcuts that might be present in the selected folders. |
| Target | Any shortcut located in selected folder will be dereferenced and its target file or folder will be treated as if it were selected. |
| Ignore | Any shortcut located in selected folder will be ignored. |
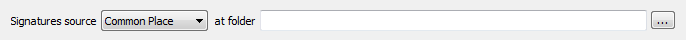
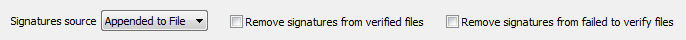
| Signatures Source Controls |
 |
|
| and also |
 |
|
|
These controls are used to tell the module where to find the file signatures.
|
| Signatures source | Select the input type and location. |
| Appended to File | Each signature is appended at the end of the signed file using the Sign Files functionality or another compatible way. |
| Common Place | All signatures are stored in the target folder and are named "[signed filename].[signed extension].signature". |
| Original Location | The signatures are located in the same folder as the signed file and are named "[signed filename].[signed extension].signature" |
| Reflecting Tree | The same directory structure as that of the selected files and folders is assumed to exist under the selected target folder. Each file signature is named "[signed filename].[signed extension].signature" and is located in the folder that reflects the folder containing the signed file. |
| at folder | Select folder to be used for the "Common Place" and "Reflecting Tree" options. |
| Remove signatures from verified files | Set this checkbox to remove the signature after a successful verification process or clear it to keep the signature appended to the file after the verification is successfully completed. |
| Remove signatures from failed to verify files | Set this checkbox to remove the signature after an unsuccessful verification process or clear it to keep the file unchanged after an unsuccessful verification. |
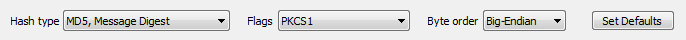
| Operation Controls |
 |
|
|
These controls are used to control the signature interpretation and must be set to the same values that were used in the file signing process.
|
| Hash type | Select the hashing algorithm: must be the same algorithm used in the file signing process or else the signature verification will fail. |
| SHA, U.S. DSA Secure Hash Algorithm | This algorithm generates a 160-bit hash value. |
| MD2, Message Digest | This algorithm generates a 128-bit hash value. |
| MD4, Message Digest | This algorithm generates a 128-bit hash value. |
| MD5, Message Digest | This algorithm generates a 128-bit hash value. |
| Flags | Select the padding: must be the same padding used in the file signing process or else the signature verification will fail. |
| PKCS#1 | Use PKCS#1 padding. |
| X.931 + PKCS#7 | Use X.931 + PKCS#7 padding. |
| Byte Order | Select the signatures byte order. Different platforms may use different byte ordering. It is important that you select the correct byte order of the signatures. |
| Big-Endian | The signatures are in Big-Endian byte order. |
| Little-Endian | The signatures are in Little-Endian byte order. |
| Set Defaults | The Set Defaults is a user-friendly button that sets the Operation Controls to a default selection of properties in order to help users who might find the settings confusing. The selection made with this button matches the Set Default selection in the Sign Files functionality window. |
| Window Controls |
 |
|
|
These controls have generic meanings.
|
| On Top | Sets and clears the Always On Top flag on the window. This checkbox adds or removes the window from the group of Top-most windows. |
| OK | Commits to work and verifies the signatures of the selected files. |
| Cancel | Closes the window without doing any work. The last selected properties are stored. |